Research estimates that up to 70% of CRM systems fail to meet expectations – and a failed CRM implementation can be extremely costly, not just in terms of the financial expense, but also because of the costs in lost time – and credibility. Even more impactful: you don’t often get a second chance at CRM success. This means that it’s critical to select the right CRM system the first time.
The good news is CRM success is more than possible. If you simply follow a few critical steps before and during the CRM selection process, you can ensure that the system you select will help you achieve your organization’s goals, enhance adoption and provide value to your users – and deliver a return on your technology investment.
Tip 1: Problems First, Then Products
When attempting to successfully select and implement CRM software, it’s essential to focus on people and processes first, products second. Too many people immediately rush out to find potential vendors, so they can set up demonstrations of the most popular CRM software.
While it’s easy to get caught up in the shiny bells and whistles of a good CRM demo, it’s important to resist the temptation to dive into features and functions too soon without first taking the time to gain a real understanding of your organizational and user needs.
Tip 2: Assess Your Needs
Organizations buy CRM software for a number of reasons – but each organization is unique. To provide real value and ROI, before making the purchase, you have to understand what you are trying to accomplish.
Start by putting together a list of the key reasons you think you need a CRM.
- Are you trying to communicate more effectively with clients and prospects?
- Manage and evaluate the ROI of events or sponsorships?
- Track and enhance business development efforts?
- Help the organization be more efficient?
- Increase business and revenue?
After assessing your organization’s needs, you may discover that you have more goals than you first thought.
If this is the case, it will be important to prioritize the goals. Don’t try to boil the ocean. If you try to tackle too many things at once, especially during the initial rollout, you will be less likely to succeed. Instead, assign your goals to a timeline based on importance and value to users. For the initial implementation, set a few relevant goals, achieve those initial successes, communicate the successes – and repeat.

Once you understand your organization’s unique needs and requirements, it’s time to talk to your users. One of the biggest frustrations we hear from clients is a lack of CRM adoption. This isn’t surprising since, in many of these organizations, system users were not involved during the selection process. To get people to buy in and use software, it has to provide value not only to the organization, but to the users individually. The challenge is that different people define value differently, which means different groups or types of users will have their own unique needs and requirements. That’s why it’s so important to get them involved early. Making your users part of the process up front will also make them more likely to adopt the software later.
To gather user input, consider creating focus groups to provide feedback on product features and functions. You may even want to meet with some of the naysayers individually to start encouraging their participation and head off future roadblocks. Finally, be sure to involve key stakeholders in system demonstrations to help evaluate the software and solicit their feedback before proceeding with system selection. In fact, it’s beneficial to have users involved throughout the rollout to offer ideas on how to improve the CRM implementation for everyone.
Tip 3: Evaluate the Systems and Providers
After gathering all the relevant information, it’s important to fully document your requirements and make sure you are well-prepared before reaching out to providers. The best way to do this is with what I call a ‘demo roadmap.’ This is a comprehensive two- to three-page document that sets out all of the details for the demonstrations along with all the needs and requirements gathered during the needs assessment and the features and functionality that you want to see.
Your ‘roadmap’ will guide the CRM providers so that they show you the key system attributes that are critical to the success of your organization and users and also helps to prevent the demonstrations from becoming a ‘dog and pony show.’ Your roadmap should be shared with the CRM providers well in advance of the demonstrations to give them time to adequately prepare.
Some larger organizations may also find it beneficial to take an additional step and create a much more detailed, formal RFP document. This request for proposals would be sent to potential CRM providers to solicit answers to a number of questions before scheduling any demos. The formal responses allow you to evaluate and compare the vendors and their system features and pricing in advance of the demonstrations. Many organizations use the RFP to limit the demonstrations to only the potential providers who are able to meet the organization’s budget and other requirements.
Once you have identified a few CRM systems that meet your requirements, you can begin the vetting process to select the right CRM system for your organization.
Tip 4: Direct the Demonstrations
It’s essential that the CRM demonstrations allow you to make an informed decision and adequately and accurately compare systems, features and pricing. It’s also important at this phase to again involve your users. CRM systems have a reputation for being notoriously difficult to implement, and the last thing you want is to be responsible for unilaterally selecting a system that then doesn’t meet user expectations. This can also help to make them more invested in system success.
It’s also important to structure the participation and demonstrations so you maximize the benefits.
First, it can be helpful to thin the field of participating CRM providers to a manageable number.
Next, select a group of users to participate. It can be good to choose users from different groups such as professionals and administrative, so you get some different perspectives.
Participants selected must have the time and inclination to participate and must be willing to sit through all of the demonstrations so they can accurately compare all the systems.
Finally, you may want to prepare the users by sharing the requirements and/or roadmap with them and asking them to be prepared to ask any questions they may have.
You should also prepare the providers. First, let them know how much time they have. A typical CRM demonstration can take between one and two hours.
Also let them know who will be participating and what their needs and interests are. If you have professional or executive users who have limited time for demonstrations, it can be helpful to direct the providers to spend the first 30 minutes to an hour of the demo on the features that are most relevant to those users.
Then they can step out and the rest of the time can be spent showing you the more detailed back-end functionality. Finally, be sure to leave at least 15 minutes at the end of the demonstrations for questions.
Tip 5: Check References
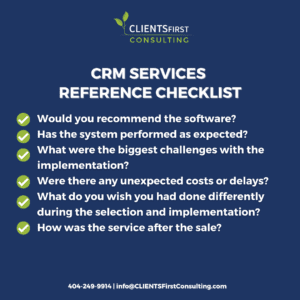
Before making the final commitment to a CRM system, it’s important to make sure you go through a thorough vetting process. It’s important to make sure you get all the information you need before finalizing your purchase.
First, ask the CRM vendor for references you can speak with. But don’t stop there. Talk to other companies or organizations in your industry who have used the software. Be sure to ask open-ended questions that will help you learn not only about the software, but also about other important areas. A few good questions to ask include:
- Would you recommend the software?
- Has the system performed as expected?
- What were the biggest challenges with the implementation?
- Were there any unexpected costs or delays?
- What do you wish you had done differently during the selection and implementation?
- How was the service after the sale?
For a comprehensive list of good questions to ask before finalizing the sale, check out our CLIENTSFirst CRM Reference Checking Questions Document.
Tip 6: Final Selection Steps
Once you have selected the right CRM system for your organization, there are still a few additional important details that require attention. You will want to have a formal scoping call with the provider to be able to accurately gauge the actual cost. The final price can vary depending on a number of variables including:
- The number and types of licenses
- Additional modules or software needed
- Professional services to implement
- Ongoing annual subscription or maintenance costs
- Any proposed integrations
- The types of training and materials
- Data conversion and/or quality
If the price is an issue with your system of choice, there are also options. First, there may be room for negotiation. Alternatively, you can do a phased rollout to spread the costs over time. Some organizations prefer to start the rollout with Marketing and power users and then roll out to a small pilot group. Then additional groups can be added in later phases over time.
Finally, remember that in any sale, you are not finished until the paperwork is done. After the price is agreed upon, you will need to review the contract or agreement. While these documents may look official and final, in fact they are often open to negotiation, so it can be beneficial to modify some of the contract terms.
For instance, if the software is new to the market, you may be able to get a discount or arrange a beta test at a reduced rate.
Additionally, instead of paying the entire invoice up front, you can often negotiate payment terms that are stepped over time based on the satisfactory completion of key deployment steps. This can enhance your chances of CRM success by aligning your CRM vendor’s success with yours.
One Last Tip: Don’t Do It Alone
Selecting the right CRM system can be a daunting process. Most firms have never been through the process before – and few want to repeat it.










